13. May 2026
Melih Abdulhayoglu’s Blog | Insights on Cybersecurity
Bring to the table win-win survival strategies to ensure proactive domination. At the end of the day, going forward, a new normal that has evolved from generation.
When the Fed and Treasury call an emergency meeting, listen On April 8, 2026, Treasury Secretary Scott Bessent and Federal Reserve Chair Jerome Powell did something almost without precedent: they summoned the CEOs of Citigroup, Goldman Sachs, Bank of America, Morgan Stanley, and Wells Fargo to an emergency session at Treasury headquarters in Washington. The […]
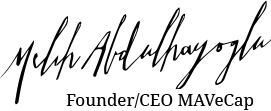
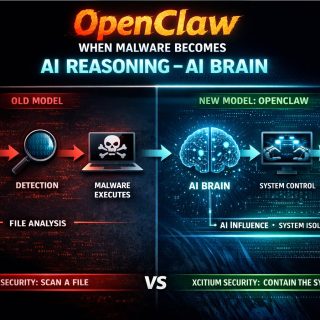
When Ransomware Lives in the AI Brain For three decades, cybersecurity operated on a stable constraint: Malicious intent had to be delivered as code. There was no alternative. If an attacker wanted to encrypt your files, steal credentials, establish persistence, or exfiltrate data, they had to ship executable instructions to your endpoint. An EXE.A DLL.A […]
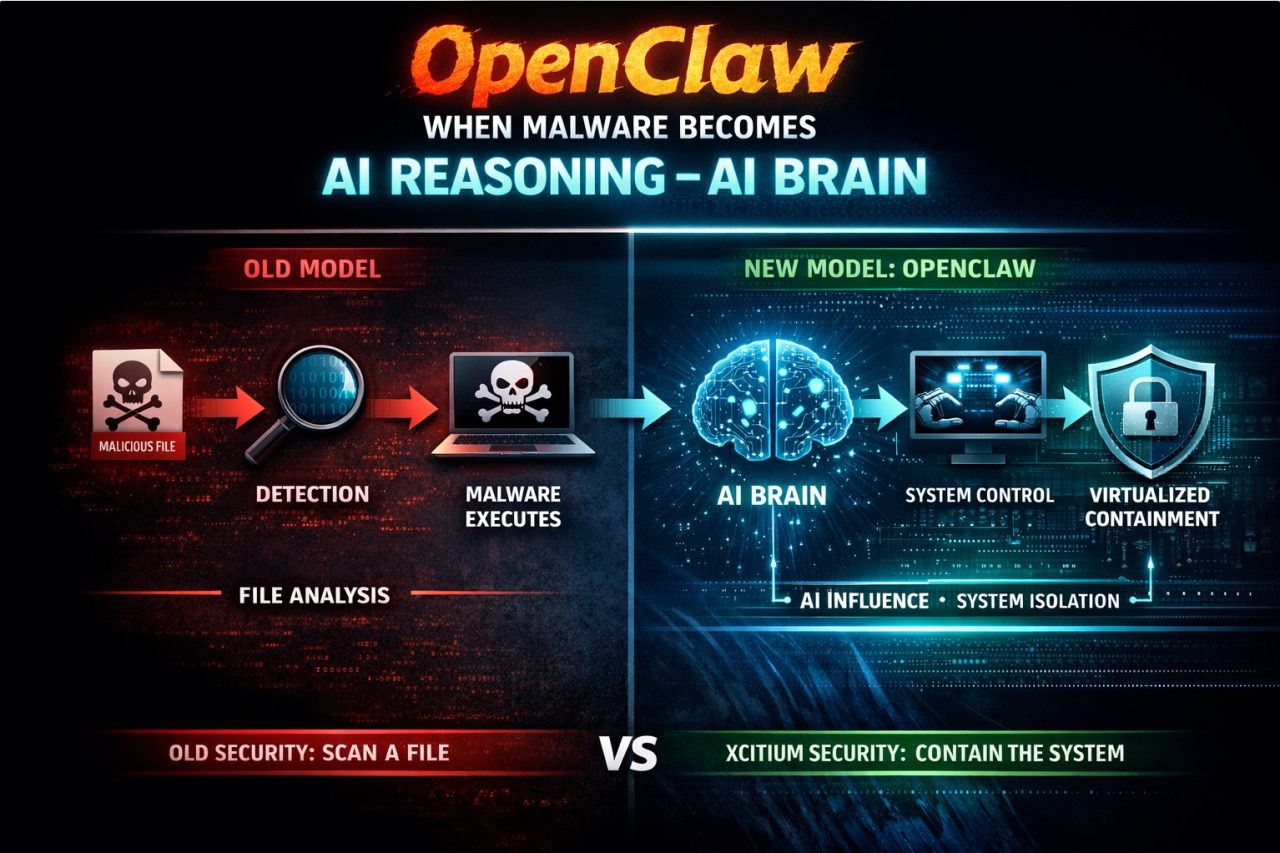
There’s an old proverb: “The axe forgets; the tree remembers.” Most people read this as a lesson about tone or delivery. It isn’t. It’s about what the axe is. A negative word is an axe. Not raised voices.Not anger.Not conflict. A single negative word — spoken casually, jokingly, or “without intent” — is an axe […]
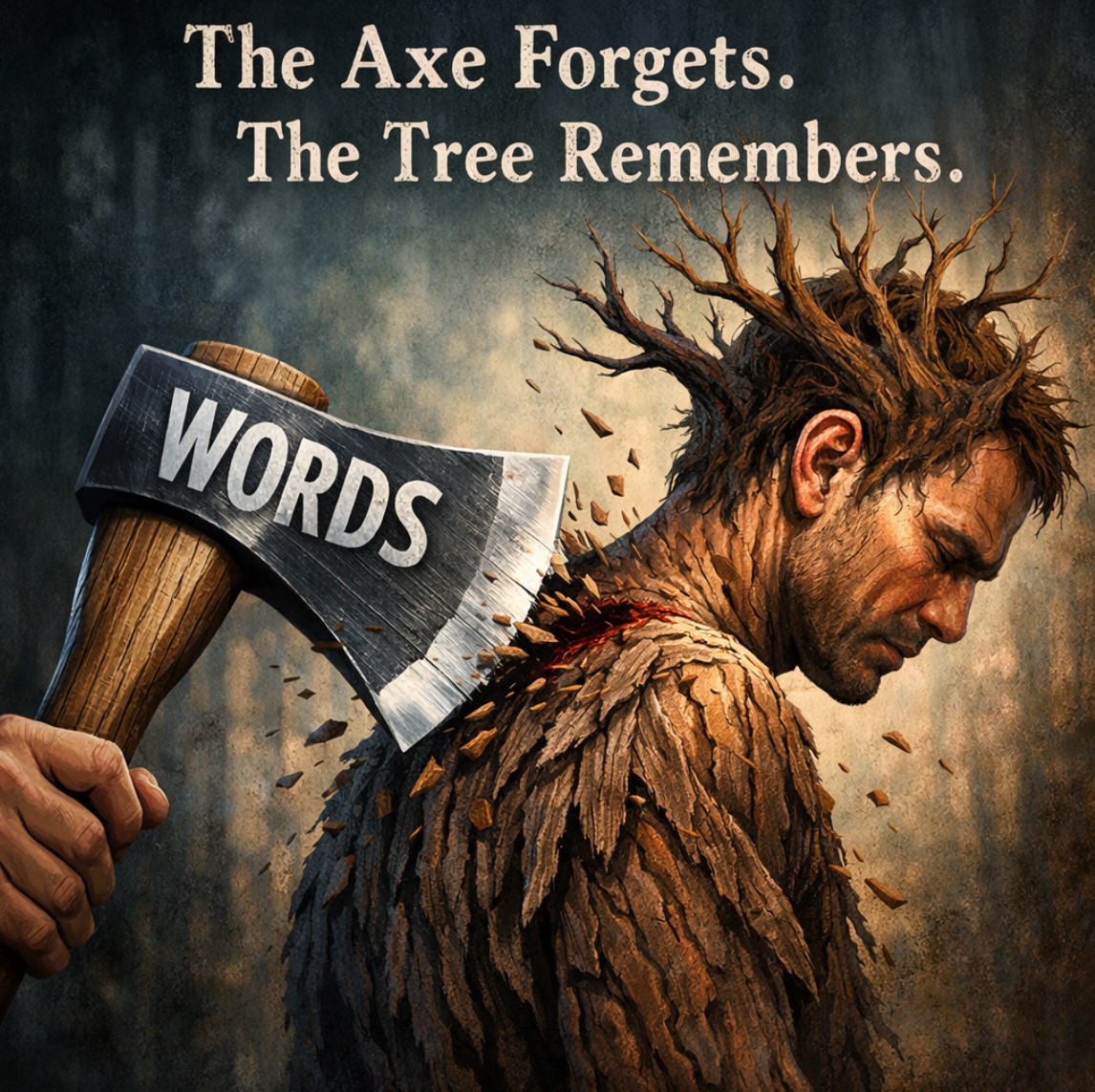
“When the winds of change blow, some people build walls and others build windmills.”— Chinese proverb 1. The Misunderstanding About Success Most people misunderstand the difference between success and failure. They think success is about: It isn’t. The real difference usually comes down to something far simpler—and far more uncomfortable: Did you hear the opportunity […]
Why perfect detection is impossible—and why claiming it miseducates the market 100% detection100% protection It sounds definitive. Reassuring.It’s also fundamentally false—not just in practice, but in theory. When a cybersecurity vendor claims 100% detection, they aren’t merely exaggerating. They are misinforming buyers, miseducating decision-makers, and setting expectations no security system—now or ever—can meet. That’s not […]
Why 90% of Rebrands Fail: The Neuroscience of Familiarity Every few years, a new CMO declares: “It’s time for a fresh look.” The logo changes.The packaging changes.The website changes. And then — sales collapse. 💥 Why?Because most rebrands break one of the most powerful forces in human behavior: 👉 Status Quo Bias — our subconscious […]
There are two truths that, if deeply understood, could reshape how we live together as human beings. Taken together, these two truths point to a profound way forward: if we accept that reality is a mental construct and that equality is the only stable social contract, we can stop fighting over “truth” and start building […]
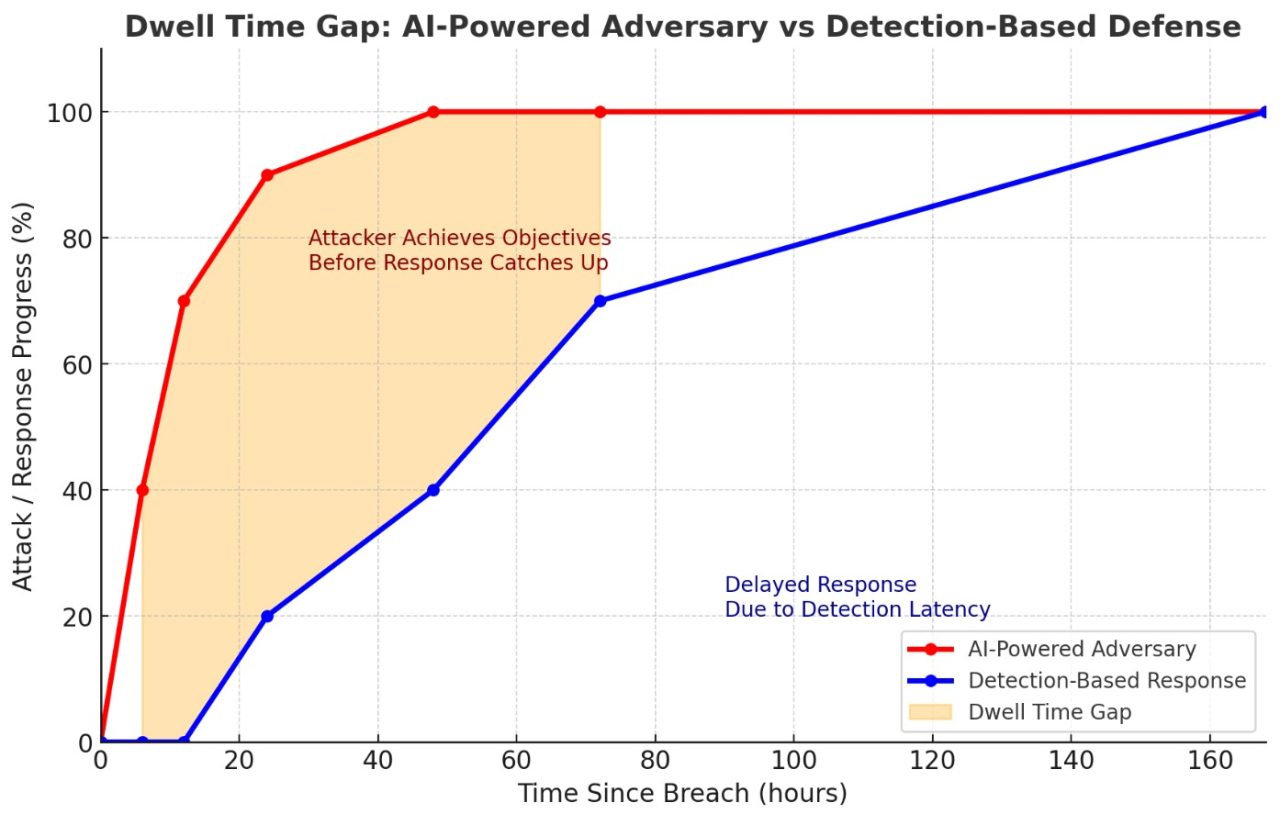
In any legacy, detection-based security model—EDR, XDR, MDR—dwell time isn’t just a historical problem. It’s built into the architecture. Here’s why it exists now, will continue to exist, and will likely get worse: The Bottom Line:As long as your protection model depends on detection before action, you are hard-coding dwell time into your defenses. With […]
🛑 $380 million.That’s the size of the lawsuit Clorox just filed against IT services provider Cognizant. The allegation?Negligence.Hackers reportedly exploited a manipulated password reset process inside Cognizant—one that bypassed Clorox’s own security protocols. The result?🚨 Corporate systems down🚨 Product shipments stalled🚨 Business continuity in shambles And now:A global brand is taking its MSP to court […]
Every few months, a new security tool promises to reduce complexity, boost visibility, or finally “unify” your cybersecurity stack. And yet, the average security team today is buried under dozens—sometimes hundreds—of tools, dashboards, and policies. We’ve consolidated, integrated, and automated. So why does it still feel like we’re drowning? The answer lies in a blind […]