24. March 2026
Melih Abdulhayoglu’s Blog | Insights on Cybersecurity
Bring to the table win-win survival strategies to ensure proactive domination. At the end of the day, going forward, a new normal that has evolved from generation.
1min4333
Hi Everyone http://www.comodogroup.com/products/comodo_security.html a bit of self promotion, but it does truly help end users. The more sites verified by Comodo the better for end users. Your help is greatly appreciated. Melih Talk Back
4min4618
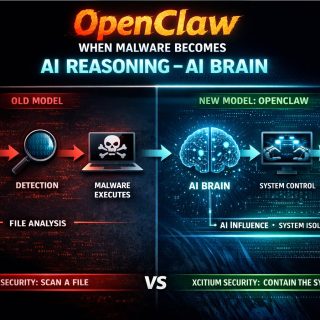
Oil Wars and CPU power! What the hell has Oil got to do with CPU power? Well they are somewhat related. One is the enabler for the physical world (Oil) and you have people fighting over it, and the other is the enabler for the Virtual world and you have people (well malware, spammers and […]
3min4532
The New Dawn: Security is not Trust Despite talk about encryption and security on the Internet, we are still falling short of true identity trust assurance every time we go online. Why? Our current attempts of encryption only encrypt our communications, but don’t check who is on the receiver. Thus giving users a false sense […]
4min4894
Well, now that we have a website www.cabforum.org, everyone knows the new standard we have been working on to improve SSL. I thought I should write a note or two to clarify few issues and make few statements 1)Where the hell this CAB forum came from? well, in April 05, I thought the time had […]
1min5022
Interesting reading. The point that is being raised in this news article is that people use AV mostly and anti spyware is yet to penetrate the market. One of the major reasons why Anti-Spyware products come as a seperate product is because vendors are looking for ways to charge extra for this. At Comodo we […]
6min4698
If you have then I strongly recommend that you go see a shrink! But imagine how your ID would feel in the midst of Bits and Bytes in your computer amongst thousands of executable programs which he does not understand, amongst the viruses that has infected your machines fighting the Trojans who is logging every […]
6min4997
Phishing is a type of fraud that is ideally suited to a lazy fraudster! After all, what work do they have to do? They don’t have to build a website, just simply copy one of the bank’s site, and they don’t have to even send the email themselves, just go to your nearest spammer who […]
9min5682
Imagine me, if you will, doing for Internet what the David Attenborough does for nature. I will consider myself utterly accomplished even if I could only achieve a small fraction of what David Attenborough has done bringing the beauty and power of nature to us I will describe the beauty and efficiency the way a […]