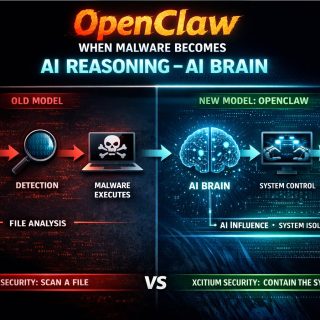
There are, in the main, two security postures in Cyber Security:
1-Allow ALL, deny BAD
2-Allow Good, deny REST
Today the vast majority of cybersecurity world works with:
(1) Allow ALL, deny BAD
They try to Deny BAD by trying to detect it by using AI,ML, Heuristic, Behavior Analysis, EDR. I must say, the results speak for itself! Breach after breach, damage after damage!
“The amount of money spent in cybersecurity” vs “Damage Sustained” is unacceptable! All because of a poor “Posture” choice!
Posture (1) is not a posture you can achieve! Its an impossible posture! You cannot DENY BAD if you don’t know its BAD!!! Mathematically impossible! Detection cannot be should NOT be, neither first nor “ONLY” method for protection!
100% Detection does not exist! Its a scientific fact! No Cybersecurity product can detect 100%!
Bottom line is “Allowing ALL’ while “Denying BAD” means when you miss a detection, you get breached! So this posture gives you a “Guaranteed Breach” mathematically speaking! Yep, Guaranteed that you will be Breached!
Ask yourself this question:
“How will you prevent the damage when your cybersecurity product fails to detect”? (no matter what Detection Method might be, AI, ML, Heuristic, Behavior, Signature or so on…they all are trying to detect something bad…and they can NEVER be 100%!)
Coming back to Posture (2) Allow Good, deny REST : is a posture you can achieve but not user friendly. Why? Because people don’t want to be restricted and want to run applications.
We need a new Cybersecurity posture that can give us the best of both worlds 1 & 2:
3- Allow Good but also Allow the REST with ASR (Attack Surface Reduction)!
Here is a brand new Security Posture, where you Allow Good, but you also Allow the REST, but in an environment with an Attack Surface Reduction.
This way you are not restricting users by denying any application from running on their computer, but you are denying any unknown ransomware, malware from causing damage because they run in a restricted (ASR) mode where they are not allowed to cause damage.
A take away thought: If you were the guy creating those ransomware would you be stupid enough to release it knowing that it will be detected right off the bat or would you first make sure its not detected, before you unleash it!!!…
IF (You still wonder why all CyberSecurity Breaches are happening)
THEN (go to the beginning of this post and read again!)
REPEAT UNTIL (you understand)